Exploiting Deserialization Vulnerabilities in Java
- 1. Exploiting Deserialization Vulnerabilities in Java HackPra WS 2015 2015/10/28 Matthias Kaiser
- 2. About Code White ▪ Pentest and Security Research Startup ▪ Based in Ulm ▪ Attacking corporate infrastructures in Red Teams ▪ Strong focus on post-exploitation ▪ Love to use 0day-angle to get initial hop ▪ AV is our best friend to gain SYSTEM ▪ Always looking for candidates ;-) 2015/10/23 2Exploiting Deserialization Vulnerabilities in Java
- 3. About me ▪ Head of Vulnerability Research at Code White ▪ Doing Technical Security for 6 years now ▪ Worked as Java Dev for a defense company ▪ Lead Expert Offensive Security at an automotive IT company ▪ Likes to find easy bugs in Java Software ▪ Found vulns in products of Oracle, IBM, SAP, Symantec, Apache, Adobe, Atlassian, etc. ▪ Enjoys low-level stuff recently ▪ @matthias_kaiser 2015/10/28 3Exploiting Deserialization Vulnerabilities in Java
- 4. Why this talk? ▪ Deserialization vulnerabilities are less known and exploited (compared to unserialize() in PHP) ▪ A dedicated bug class on its own ▪ Only a few researchers disclosed deserialization vulnerabilities like Takeshi Terada, @djorm, @gebl & @frohoff, etc. ▪ Easy to spot, easy RCE if the right classes are in the classpath ▪ I spent research time of CW to analyze several products of Oracle, Atlassian, Apache, etc. ▪ Only my Atlassian Bamboo vulnerability is patched, more RCEs to come ☺ 2015/10/23 4Exploiting Deserialization Vulnerabilities in Java
- 5. Disclaimer ▪ This is not a reference how Serialization works, I skip details for speed. Read the spec. ▪ This talk does _not_ cover Privileged Deserialization (from @samikoivu) used to escape the JVM Sandbox ▪ Custom Serialization Frameworks like XStream, Castor etc. won’t be discussed although the exploitation vectors shown here can be applied to XStream 2015/10/23 5Exploiting Deserialization Vulnerabilities in Java
- 6. Agenda 2015/10/23 6 1 What is serialization? 2 What‘s the issue? 3 How to exploit it? 4 Where is serialization used? 5 Case-Study: CVE-2015-6576 Exploiting Deserialization Vulnerabilities in Java
- 7. 1 What is serialization? To serialize an object means to convert its state to a byte stream so that the byte stream can be reverted back into a copy of the object (x) 2015/10/23 7Exploiting Deserialization Vulnerabilities in Java (x) https://docs.oracle.com/javase/tutorial/jndi/objects/serial.html
- 8. 1 What is serialization? 2015/10/23 8Exploiting Deserialization Vulnerabilities in Java
- 9. 1 What is serialization? 2015/10/23 9Exploiting Deserialization Vulnerabilities in Java
- 10. 1 What is serialization? Class java.io.ObjectOutputStream ▪ Writes serialized data to an OutputStream ▪ Has methods writeObject(), writeChar(), writeShort(), writeUTF(), etc. Class java.io.ObjectInputStream ▪ Reads serialized data from an InputStream ▪ Has methods readObject(), readChar(), readShort(), readUTF(), etc. 2015/10/23 10Exploiting Deserialization Vulnerabilities in Java
- 11. 1 What is serialization? Customizing serialization ▪ Developers can customize how objects are serialized to bytes /deserialized from bytes ▪ Serializing 1. writeReplace() → Developer can provide a replacement object to be serialized 2. writeObject() → Full control over what will written to the stream ▪ Deserializing 1. readObject() → Full control over what will be read from the stream 2. readResolve() → Replacing a deserialized object with another one 2015/10/23 11Exploiting Deserialization Vulnerabilities in Java
- 12. 1 What is serialization? 2015/10/23 12Exploiting Deserialization Vulnerabilities in Java
- 13. 1 What is serialization? 2015/10/23 13Exploiting Deserialization Vulnerabilities in Java
- 14. 2 What‘s the issue? ▪ ObjectInputStream does not check which class gets deserialized ▪ There is no whitelist/blacklist which classes are allowed to get deserialized ▪ All serializable classes that the current classloader can locate and load can get deserialized ▪ Although a class cast exception might occur in the end, the object will be created! ▪ User supplied input can be processed in readObject()/ readResolve() ▪ If a class does something “dangerous” in readObject()/ readResolve() it might get abused ▪ Case-Study: Apache Commons FileUpload (CVE-2013-2186) 2015/10/23 14Exploiting Deserialization Vulnerabilities in Java
- 15. 2 What‘s the issue? Apache Commons FileUpload ▪ Makes your life easy when dealing with HTTP file uploads ▪ Just add to your webapp and uploads are easy CVE-2013-2186: ▪ But requires the null-byte vulnerability, patched in Java 7u40 or Java8 2015/10/23 15Exploiting Deserialization Vulnerabilities in Java
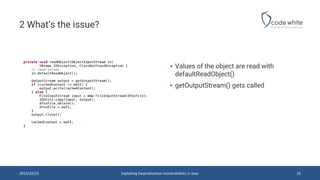
- 16. 2 What‘s the issue? ▪ Values of the object are read with defaultReadObject() ▪ getOutputStream() gets called 2015/10/23 Exploiting Deserialization Vulnerabilities in Java 16
- 17. ▪ Calls getTempFile() ▪ Creates new File ▪ repository is a member of the class under our control ▪→we can put a u0000 at the end of repository path 2 What‘s the issue? 2015/10/23 Exploiting Deserialization Vulnerabilities in Java 17
- 18. 3 How to exploit it? ▪ Finding ObjectInputStream.readObject() calls on user supplied input is easy ▪ You can decompile and grep for it … / “Open Call Hierarchy” in Eclipse ☺ ▪ The question is how you can turn a ObjectInputStream.readObject() call into RCE ▪ Several universal exploitation vectors exist: ▪ Spring Framework <=3.0.5, <=2.0.6 (cve-2011-2894 of @woutercoekaerts) ▪ Groovy < 2.4.4 (cve-2015-3253 of @gebl & @frohoff) ▪ Apache Commons Collection (cve-xxxx-xxxx of @gebl & @frohoff) ▪ More to come … (e.g. cve-xxxx-xxxx of @matthias_kaiser) ▪ @gebl & @frohoff were so kind and published “ysoserial” to make exploitation easy … ▪ Let’s find out how an universal exploit for Apache Commons Collection works 2015/10/23 18Exploiting Deserialization Vulnerabilities in Java
- 19. 3 How to exploit it? Apache Commons Collection Exploit ▪ I adapted the one from @gebl /@frohoff to skip what a java.lang.reflect.Proxy is ☺ ▪ It’s just AWESOME, because Commons Collection is almost everywhere in the classpath ▪ Disclosed 274 days ago at AppSec California 2015, still not patched ▪ Self-executing, just send the stream and wait for ObjectInputStream.readObject() ▪ The vulnerabilities are in several Collection implementations (Map, Set, etc.) ▪ A TransformedMap can be created that invokes methods via reflection (=dynamically) ▪ An InvocationHandler from the “sun.”-namespace is used to trigger the vulnerability 2015/10/23 19Exploiting Deserialization Vulnerabilities in Java
- 20. 3 How to exploit it? 2015/10/23 Exploiting Deserialization Vulnerabilities in Java 20 ▪ The TransformedMap transforms keys/values when stored into the map (put(), putAll()) ▪ Therefore the keyTransformer/valueTransformer are invoked ▪ All elements of the Map are stored in a set of Map.Entry objects
- 21. 3 How to exploit it? 2015/10/23 Exploiting Deserialization Vulnerabilities in Java 21 ▪ When the value of a Map.Entry object is changed, the valueTransformer is invoked
- 22. 3 How to exploit it? 2015/10/23 Exploiting Deserialization Vulnerabilities in Java 22 ▪ Transformers can be chained using a ChainedTransformer
- 23. 3 How to exploit it? 2015/10/23 Exploiting Deserialization Vulnerabilities in Java 23 1. Constructor takes the method to invoke, argument types and the arguments 2. Invokes the method on the input object and returns the method return value 1 2
- 24. 3 How to exploit it? 2015/10/23 Exploiting Deserialization Vulnerabilities in Java 24 ▪ Now we need a serializable class that calls Map.Entry.setValue() in a readObject() or readResolve() method to get code execution
- 25. 3 How to exploit it? 2015/10/23 Exploiting Deserialization Vulnerabilities in Java 25 ▪ Member type is of class Class, memberValues of class Map! ▪ Constructor is package-private and performs some checks before setting the members
- 26. 3 How to exploit it? 2015/10/23 Exploiting Deserialization Vulnerabilities in Java 26 1. Read in default values (type, memberValues) 2. type is a annotation type. We can use java.lang.annotation.Target.class 3. memberValues is a map implementation of our choice 4. memberValue is a of Map.Entry 5. If our map contains an entry like (“value”,”value”) we can pass the checks 6. memberValue.setValue is invoked! 1 2 34 5 6
- 27. 3 How to exploit it? 2015/10/23 Exploiting Deserialization Vulnerabilities in Java 27 1. Since the constructor of AnnotationInvocationHandler is package-private, we need to make it accessible/callable using reflection 2. We create a new instance using our parameters with reflection1 2
- 28. 3 How to exploit it? No Groovy or Commons Collection in the Classpath? ▪ Look for readObject(), readResolve() doing „nasty“ things ▪ Java has the concept of Proxies that forward method calls to InvocationHandler ▪ So take another look for serializible InvocationHandler, because they often do reflection magic on user input ▪ There is more to come, several researchers are working in this topic ▪ As soon as my vulnerabilites are fixed I will release the vectors on our blog/github 2015/10/23 28Exploiting Deserialization Vulnerabilities in Java
- 29. 4 Where is Serialization used ▪ Remote Method Invocation (RMI/JRMP) ▪ Custom RMI/IPC protocols (e.g. Spring HTTP invoker, …) ▪ Java Management Extension (JMX) ▪ Java Messaging Service (JMS) 2015/10/23 29Exploiting Deserialization Vulnerabilities in Java
- 30. 5 Case-Study: CVE-2015-6576 2015/10/23 30Exploiting Deserialization Vulnerabilities in Java
- 31. 5 Case-Study: CVE-2015-6576 ▪ Bamboo is a continuous build server from Atlassian ▪ Just did a grep for readObject() on the source ▪ One hit which looked interesting: DeliverMessageServlet 2015/10/23 31Exploiting Deserialization Vulnerabilities in Java
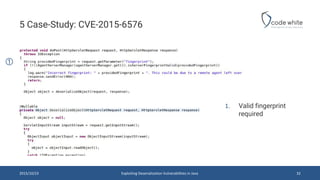
- 32. 5 Case-Study: CVE-2015-6576 2015/10/23 32Exploiting Deserialization Vulnerabilities in Java 1. Valid fingerprint required 1
- 33. 5 Case-Study: CVE-2015-6576 ▪ We need a valid fingerprint ▪ Atlassian Bamboo uses Struts ☺ ▪ There is an action “GetFingerprint” that can be invoked via HTTP request ▪ We have some check but let’s see how easy it is to bypass them 2015/10/23 33Exploiting Deserialization Vulnerabilities in Java
- 34. 5 Case-Study: CVE-2015-6576 2015/10/23 34Exploiting Deserialization Vulnerabilities in Java 1 2 3 4 5 1. Authentication is checked 2. If we are an Elastic Agent we pass 3. We are an Elastic Agent if our agentType is “elastic” 4. Again! 5. Get the fingerprint
- 35. 5 Case-Study: CVE-2015-6576 2015/10/23 35Exploiting Deserialization Vulnerabilities in Java DEM O
- 36. 5 Case-Study: CVE-2015-6576 2015/10/23 36Exploiting Deserialization Vulnerabilities in Java
- 37. 5 Case-Study: CVE-2015-6576 2015/10/23 37Exploiting Deserialization Vulnerabilities in Java